With cyber-attacks on the rise, we take a look at how and why they happen and what we can do to protect ourselves.
One of the largest cybersecurity attacks on US infrastructure devastated a fuel pipeline and cut oil supplies to much of the East Coast.
 ADVERTISEMENT
ADVERTISEMENT
 ADVERTISEMENT
ADVERTISEMENT
The ransomware attack on the Colonial Pipeline, the US's largest fuel pipeline, took the company offline and could see petrol prices rise if the situation is not resolved in the next few days.
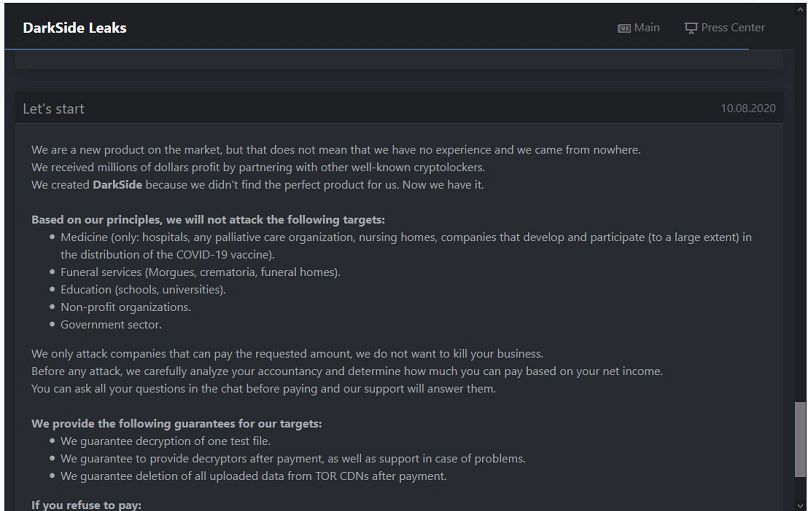
The hacker group responsible, DarkSide, believed to be based in Russia, issued an apology on Monday, saying its goal was not in "creating problems for society" but "to make money".
But the disruption has become a geopolitical issue. President Joe Biden said there was no evidence “so far” that the Russian government had any involvement in the hack. But he said Russia “has some responsibility” to deal with ransomware attacks that occur from its soil.
With cyber attacks on the rise, we take a look at how and why they happen and what we can do to protect ourselves.
How do cyber attacks happen?
Details about how the attackers hacked the US pipeline are still unknown. But the Colonial Pipeline said its systems were attacked on Friday, which is a typical day for cybercrime activity as they can exploit the weekend when security staffing is not at full capacity.
Typically, hacking occurs in two ways.
The first is by exploiting human vulnerabilities so that people open malicious emails.
"The attackers would try to elicit strong emotions like fear of urgency or excitement in order to trick the victim into opening a malicious link and then download the attachment," said Stefano De Blasi, a threat researcher at the online risk protection company Digital Shadows.
The second way, De Blasi told Euronews, is by exploiting "software vulnerabilities on products that were not punched properly and then left an open door for the attackers to come in".
Given how DarkSide has operated in the past, it is also possible that the attackers gained entry to the Colonial Pipeline networks by buying remote access from Initial Access Brokers (IABs), De Blasi said.
IABs work as the “men-in-the-middle” and work by providing ransomware groups with a pool of victims to target.
Why do ransomware groups attack?
Ransomware groups carry out their attacks for profit and non-political reasons.
DarkSide said on its data leak website on May 10 that they are not affiliated with any government and are solely financially motivated.
DarkSide is believed to operate from Russia based on its victims' pool as many hacker forums state they should not attack their citizens. Some language traits also indicate the operators are native Russian speakers.
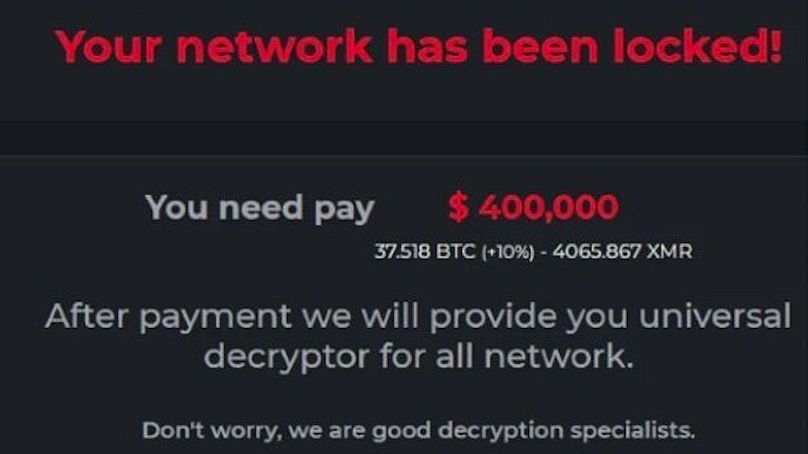
Cybercriminals can make eyewatering amounts of money by getting access to sensitive information and threatening to release it public on the condition of a ransom payment.
It is difficult to assess how much ransomware groups make as only a fraction of attacks are made public. But Di Blasi points to a recent attack on a major electronics company that reportedly resulted in a $50 million (€42 million) ransom request.
In March, the FBI's Internet Crime Complaint Centre said there were 2,474 cybercrime incidents reported last year with a total victim loss of $29 million (€23 million). But many experts say the figure is believed to be much higher.
Increasing attacks
The Colonial Pipeline is not the first attack of its kind. In April, a hacker gained access to the Oldsmar water treatment facility in Florida and tried to increase the level of sodium hydroxide. Thankfully, no one was harmed as fail-safes were in place and operators could reduce the levels to normal.
In 2015, hackers in Ukraine accessed a power plant and were able to cut electricity to hundreds of thousands of people.
"We are seeing an increase in the number of fronts where attacks upset a number of fronts, both groups operating in business," said Di Blasi.
Since 2019, hackers have been resorting to double extortion methods, he added, where they get access to a network, create data and then exfiltrate the data and threaten to release it publically if the ransom is not paid.
How can we prevent cyber hacking?
"No system is 100 per cent secure," said De Blasi but there are several steps we can take to improve our protection.
The first one, he says, is companies should increase training and raise awareness of cyber threats.
"It is the first step and it's a crucial one because it can really make a difference in the long term," he said.
The second step is to improve the system update for software and try to mitigate every vulnerability in your system to complicate the efforts of hackers.
A global defence
But it is not just companies who need to boost their security practices against cyber threats. Disrupting ransomware groups is also not easy as the affiliates are dispersed across several countries and made up of subgroups.
"The cybersphere is a sort of grey zone at the moment in terms of attack and therefore can serve in a sort of way to avoid international legislation," said De Blasi.
"Strengthening the partnerships between governments and their efforts to increase the resilience of their cybersecurity is definitely a key step in defence".
Attacks on national infrastructures are a huge concern.
Last month, the global coalition of experts called the Ransomware Task Force warned of a "national security risk" and urged governments to take action against ransoms being paid in secret.
The group also wants pressure to be put on countries, such as Russia, North Korea and Iran, which are often accused of accommodating ransomware groups.
But combined international efforts have worked.
In January, law enforcement agencies in Bulgaria and the US disrupted infrastructure associated with the ransomware Netwalker. Authorities seized a server reportedly used to host dark web pages for victims to communicate with Netwalker’s operator.
The data leak site is still inactive and there has been a drop in Netwalker activity.
In February, affiliates of the “Egregor” ransomware were reportedly arrested in Ukraine. Investigators had seemingly tracked Bitcoin transactions made by the individuals, which led to their arrest.
While there is no guarantee these law enforcement operations will stop these groups in their tracks, it is likely to make other ransomware groups nervous.
Europe, too, has bolstered its efforts in fighting cybercrime.
On Monday, the European Commission announced it will make €11 million of funding available for 22 new projects seeking to strengthen the European Union's capacity to deter and mitigate cyber-threats and incidents.
It aims to do this by employing the latest technologies.