In the second part of our investigation, Euronews Next unpicks how an international jobs scam targeting thousands of people is relying on cyber slavery.
"You think I scam you $30 [€28] for the time that I spent training you to proceed with this job?" asked "Stella," a WhatsApp scammer Euronews Next has made contact with.
 ADVERTISEMENT
ADVERTISEMENT
 ADVERTISEMENT
ADVERTISEMENT
Posing as a new "employee," Euronews Next had been "working" with Stella, reportedly a London-based recruiter for a commerce platform called Digital Logic, as part of an investigation into a prolific global recruitment phishing scam.
Stella was trying to convince us to convert US dollars into Tether (USDT), a cryptocurrency tied to the dollar's value, and transfer the amount to Digital Logic, a platform on which we were supposedly making money.
In our first week of "employment," we took a 0.6 per cent commission and made 800 USDT, according to the platform, but we had to "reset" our account and add 30 USDT if we wanted to keep working.
When Euronews Next repeatedly asked Stella why this was necessary and whether it was a scam, she became defensive and highlighted the fact she was only asking us for a small amount.
By then, however, Euronews Next had already spoken to fraud experts who detailed the scam and explained that amounts required to "reset" were doubled each week.
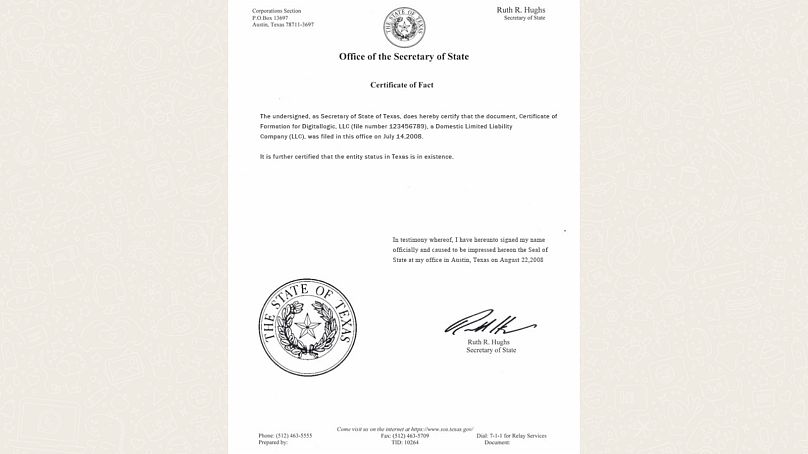
While experts had already confirmed to us that Digital Logic was part of a broader network of scams, according to a document on the company’s website, the firm was incorporated in Texas in the United States on July 14, 2008.
Euronews Next reached out to the Texan Secretary of State’s spokesperson who disagreed: there was a company with the same name in the state, but it was created well before 2008 and this document was forged.
Digital Logic is far from being the only company with a fake online presence, according to a new report by AI cybersecurity company CloudSEK. Its authors have found that over 1,000 firms are being targeted by this particular scam.
"We were conducting AI brand monitoring for a large client, when we picked up a lot of fake domains for them," said Koushik Sivaraman, vice president at CloudSEK.
"What we discovered is how well-organised the scammers are, how widespread, and how fluid they are in terms of operational security," he told Euronews Next.
He and his team have named the scam WebWyrm, in reference to a mythological dragon, and believe that it has already extracted over €100 million from more than 100,000 victims, according to their projections.
Where are scammers getting our numbers from?
While CloudSEK is still looking into how scammers got hold of hundreds of thousands of phone numbers, they believe some of them come from job board leaks because some messages refer to applications that candidates have made on those.
The recruitment companies used as aliases by the scammers, however, maintain that they haven’t been hacked.
According to experts at non-profit JobsAware, to whom Euronews Next spoke for the first part of this investigation, phone numbers targetted by this scam don’t necessarily correspond to clients of big firms such as Adecco or Hays and Reed which are being impersonated by scammers.
"Your phone number was not part of a data breach at Totaljobs and your data continues to be safe with us," said an early October email the recruiter sent to clients, which Euronews Next had access to.
Others suspected a breach from WhatsApp, which was accused of leaking 500 million numbers in May and on which most of this scam was unfolding.
A spokesperson from the Meta-owned company has told Euronews Next, however, that they had not been targeted by a hack and that the claims were baseless.
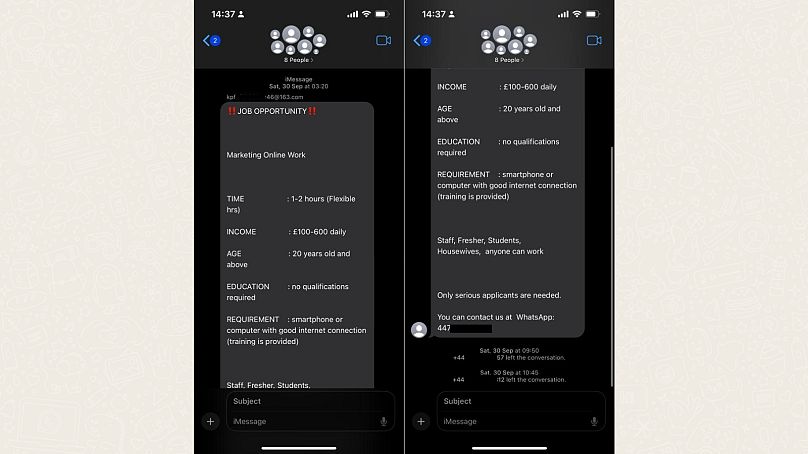
Reports of scam messages received on iMessage have also started emerging, further complicating the search.
"Everybody says, 'we’ve already seen this sort of scam,' but I think people are not aware of the scale at which this scam operates," explained Sivarman from CloudSEK.
The firm is in touch with global law enforcement agencies, who “initially weren’t surprised” but had a change of heart when they realised the fraud’s scope.
Euronews Next contacted Europol, Interpol, and the FBI in the course of this investigation. While the first organisation said it couldn’t confirm or deny it was working on WebWyrm, Interpol replied to our inquiries by saying that it didn’t have any information to "share at this stage".
The FBI didn’t provide much more clarity on the origin of the data of victims, only remarking that its Internet Crime Complaint Center division had received "over 500 employment scam complaints reporting the use of WhatsApp, filed by complainants from more than 60 countries".
Is China behind WebWyrm?
CloudSEK spent six months uncovering the WebWyrm network, and while their work is ongoing, they say they’ve already found over 6,000 websites related to the scam.
"When abuse reports arise, scammers swiftly transition to new infrastructure," ensuring "sustained anonymity and operational continuity," the firm’s new report read.
According to researchers, perpetrators elude detection by regularly changing the IP addresses of their platforms.
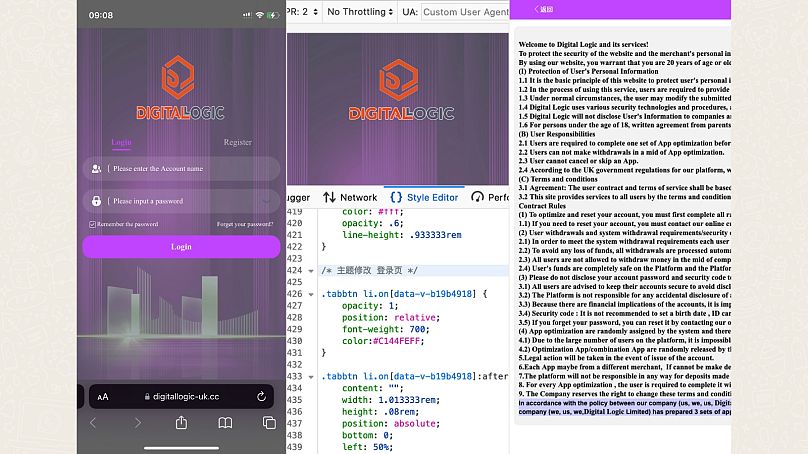
CloudSEK highlights similar patterns among these websites, including being mobile-first, being named after a set of keywords (as is the case with the name of Euronews Next’s "employer," Digital Logic), and requiring a login page to gain full access to the platform.
Anuj Sharma, a security researcher at CloudSEK and an author of the WebWyrm report, has found that websites correspond to 119 IP addresses grouped on 12 autonomous system numbers (ASN), a network to host IPs.
"The orchestrators are, of course, one single group," Sharma told Euronews Next. Two of the 12 ASNs he has identified are based out of China and "have previously been involved in frauds such as crypto scams," according to the researcher.
All websites contain "Chinese language or references in the source code" and Sharma has further identified that 800 websites have been built on ThinkAdmin, a Chinese backend framework.
CloudSEK can’t attribute WebWyrm to one group with confidence, but told Euronews Next that it believes the scam might be orchestrated by groups of Chinese origin.
Meanwhile, as investigations are ongoing and the perpetrators are being scrutinised, copy-cat scams are popping up and orchestrators are pivoting techniques, with an increasing number of websites hosted on American IT company CloudFlare, which can hide IP addresses, Sharma explained.
Is this scam based on cyber slavery?
“We were very surprised at the scale at which this scam is happening, and the regional tailoring perpetrators were doing,” CloudSEK vice president Sivarman said.
His team have found reference to over 600 WhatsApp numbers from around the world in the code of scamming websites.
According to CloudSEK, scammers most likely have phone farms with endless rows of phones, or use SIM boxes, gateways from which they handle several SIM cards.
They also believe perpetrators set up virtual international numbers via easily available services. But they don’t stop there.
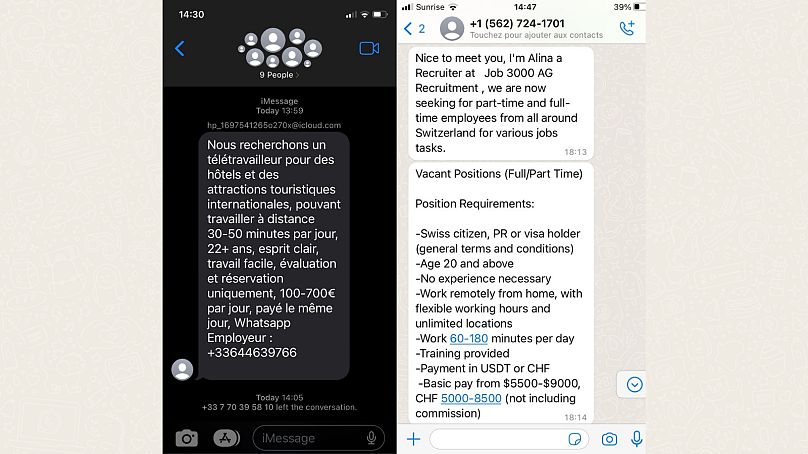
"When you’re in the US, you get a message saying you can earn in dollars, but in India, you’ll get a message saying it’s rupees. So scammers cater for currency, for local awareness, and the fake domains they create even have prefixes or suffixes to help them bucket them into various regions," Sivarman explained.
While the scam mostly targeted British and Australian numbers at the start, people from Italy, France, and Switzerland are now also flagging this scam, according to Euronews Next’s own investigation.
The tailoring and massive scale of human interactions prompted Sivarman’s team to look into how such an operation could be conducted.
"That’s when we linked this to cyber slavery," said Sivarman.
According to social enterprise Humanity Research Consultancy (HRC), cyber slavery has reached never-before-seen levels.
"While getting spammed with fraudulent messages is now an everyday occurrence, this inconvenience may actually be rooted in a malignant new form of modern slavery," said their report on the topic.
HRC has documented compounds set up by traffickers around South East Asia and Dubai, and which are now also developing in Latin America.
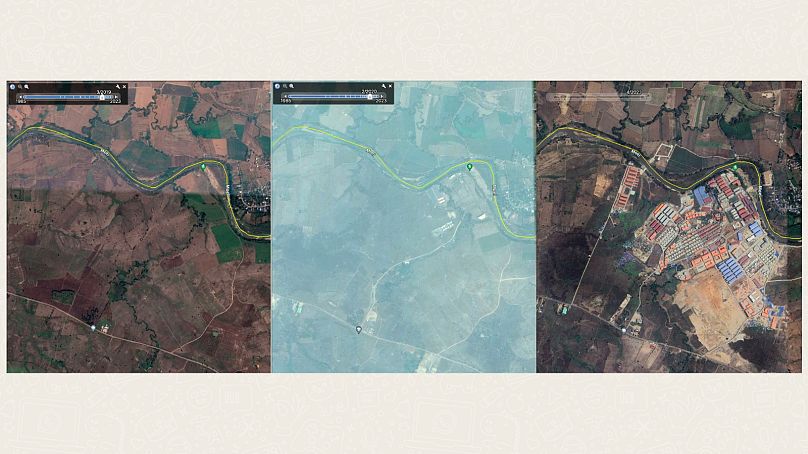
In Myanmar, about 20 compounds are set up in Myawaddi, close to the Thai border - with KK Park being the most notorious - while in Cambodia, Sihanoukville, which is a development of the Chinese One Belt One Road Initiative, has been identified as one of the main hubs for cyber slavery.
According to the government of Cambodia, the Sihanoukville Special Economic Zone - on the outskirts of the city - is "constructed by Chinese and Cambodian enterprises" and "is aiming at creating an ideal investment platform for enterprises".
While this may have been the case initially, HRC believes that Cambodia’s ban on gambling in 2019 and the COVID-19 pandemic have resulted in the departure of many investors, who have left room for Chinese organised crime groups.
Today, in the "predominantly Chinese-operated city," casinos are turned into compounds.
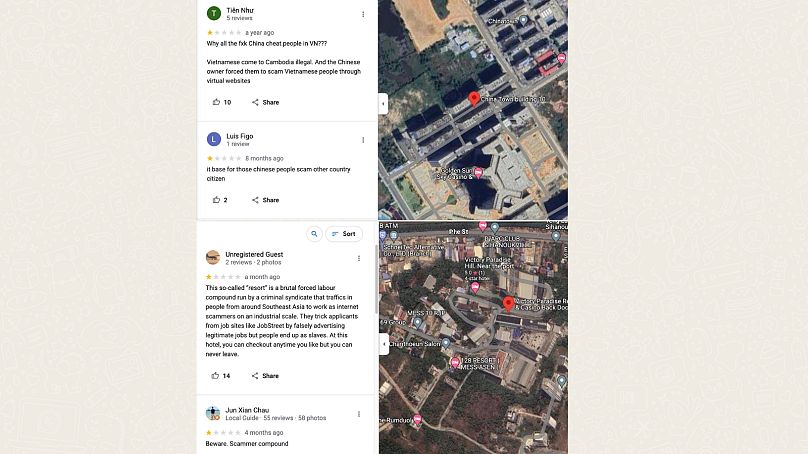
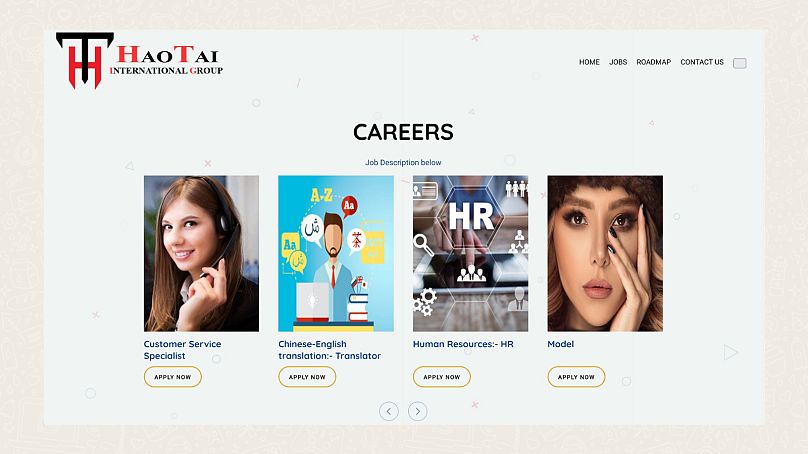
Perpetrators attract victims from all over the continent, including China, Vietnam, and Bangladesh, by advertising roles in customer service, product service, and online gaming on job portals or social media.
According to HRC, victims are usually between 18 and 30 years old and while they might initially enter the compound willingly, once they start working, they usually can no longer leave, have their passports confiscated, and face the prospect of torture if they don’t comply.
Victims are also "openly sold between employers/enslavers," said HRC’s report.
The detained people are forced to scam others via social media or messaging services such as WhatsApp and specific skills, such as speaking English, are required, depending on the nature of the fraud.
Valentina Casulli, the head of operations at HRC, has been looking into WebWyrm’s setup since February 2023.
While she was suspicious that the scam was fuelled by cyber slavery, she only got confirmation two weeks ago.
“We received information from a victim who was in a compound in Dubai. He was trafficked there and had to scam people into carrying out a certain number of tasks on a website,” she told Euronews Next, referencing WebWyrm’s modus operandi.
A second compound victim in Myanmar also described the same scam.
Stella, from Digital Logic, said she was in London but Euronews Next was unable to acquire a photo on request to confirm her identity or location.
When we suggested reaching out to NGOs working on human trafficking if she was unsafe, Stella answered, "I don’t understand what are you talking about".
‘A transnational crime needs a transnational response’
According to Casulli, close to a million people are currently being held in compounds. While they may be forced to conduct WebWyrm operations, the expert believes they most likely also perform other sorts of fraud, such as long-term scams known as pig butchering that involve romance and crypto.
Compounds are usually owned by a person who rents them out to companies managing the cyber slaves and owners sometimes pay bribes to local authorities, according to HRC, which will release a briefing on the link between WebWyrm and cyber slavery in the coming weeks.
"This is a link in a chain of huge criminal operations," said Casulli, explaining that money gained from scams such as WebWyrm could finance illegal gambling, drug trafficking, and sexual exploitation.
"The money is laundered, and it just disappears. It’s untraceable,” she added.
The fact that earnings are made in crypto further complicates the pursuit of funds, and the funding of terrorist activities using Tether has recently surfaced.
While compounds are gaining momentum in the public eye, with Chinese film No More Bets topping the box office this summer and Interpol flagging them as an Orange notice in June, the researcher says more needs to be done to stop this “global security threat”.
In its recently released report, the United Nations Office on Drugs and Crime (UNODC) highlights many shortcomings of local authorities, such as corruption and lack of means, but mentions that the Association of East Asian countries (ASEAN) and China has put together a "comprehensive, detailed plan of action," which will be presented soon.
According to Casulli, the responsibility also lies with Western states.
"This is a transnational crime, which needs a transnational response," she said and added "it also shows the role that the finance industry, banks, and tech industry have to play. It's not enough being a counter-trafficking expert, you also need cyber experts, finance and crypto experts, and law enforcement".
According to CloudSEK’s report, British companies and citizens are the hardest hit by this scam, and while the government has been taking action against scams, Casulli feels it’s still not doing enough about compounds.
"The fact that we've managed to link this scam to the compounds shows that the UK needs to do something about human trafficking too because it is being impacted," she said.
Beyond financial losses, experts also highlight the emotional plight of such scams. “He killed himself a month after I talked to him,” said Troy Gochenour, from the Global Anti Scam Organisation (GASO), about a British person who had been scammed over €100,000.
"Law enforcement is barely keeping up with pig butchering scams and that’s maybe why we're not hearing so much about the job scam," Gochenour told Euronews Next. The volunteer, who himself was once a victim of a scam, is hopeful that actions will be taken to protect people.
"Before that happens though, there's going to be a lot more funds that are going to be stolen, likely not to be returned," he said.
This article is the second in a two-part investigative series. In the first part, find out how Euronews Next unravelled the scam which has already embezzled an estimated €100 million from victims.